Your Security Program Is Not Mythos-Ready. Here’s How to Fix That.
Deconstructing the AI vulnerability storm — what actually changes, what doesn’t, and what to do about it. Back to basics!
The AI vulnerability storm changes the speed and scale of the threat. It does not change the fundamentals of good security. Your five NIST functions still matter.
The gap between attacker speed and defender speed is real. You will not close it by working harder. You will close it by building differently.
Hello Cyber Builders 🖖
Mythos made headlines on social media recently. Public cybersecurity company valuations dropped. The market responded to the idea that if AI can replicate what CrowdStrike and Tenable built in years, the value proposition changes.
The argument is strong. I see why it affects the market.
But this view oversimplifies what security involves.
In my previous post, I argued that Mythos wasn’t a breakthrough. It was the moment the exponential became visible to everyone outside the security community. The capability curve had been bending for over a year — XBOW topping HackerOne, Google Big Sleep autonomously finding zero-days, DARPA AIxCC scanning 54 million lines of code in four hours. Mythos just made it legible to boards and mainstream press.
This shifts the discussion, but it does not change the core work of security.
In this post, I will focus on practical steps.
I will outline daily security tasks, show where AI changes each function, and describe what a Mythos-ready program looks like in practice.
Security is not just vulnerability detection
The cybersecurity conversation often reduces the field to a few capabilities. Currently, the focus is on 'AI finds all the bugs.' But bug discovery is only one part of a larger system.
Security work follows five main areas, as defined by the NIST Cybersecurity Framework:
Identify: Know your assets, your attack surface, and your exposure.
Protect: Put safeguards in place to reduce the likelihood of incidents.
Detect: Discover anomalies, vulnerabilities, and active threats — fast.
Respond: Contain and mitigate incidents when they happen.
Recover: Restore operations and prevent recurrence.
Mythos primarily demonstrated a major advance in detection, particularly in automated vulnerability discovery at scale. The model found thousands of zero-days across major operating systems and browsers. It produced 181 working Firefox exploits, compared to two from Claude Opus 4.6. This is a significant leap.
Detection is only one part. Attackers still need to exploit, pivot, move laterally, and exfiltrate data. The goal is to make each step more difficult and to detect, respond, and recover faster than attackers can act.
The real question is not whether Mythos makes CrowdStrike obsolete. Which of your five security functions are now underpowered, and what needs to change?
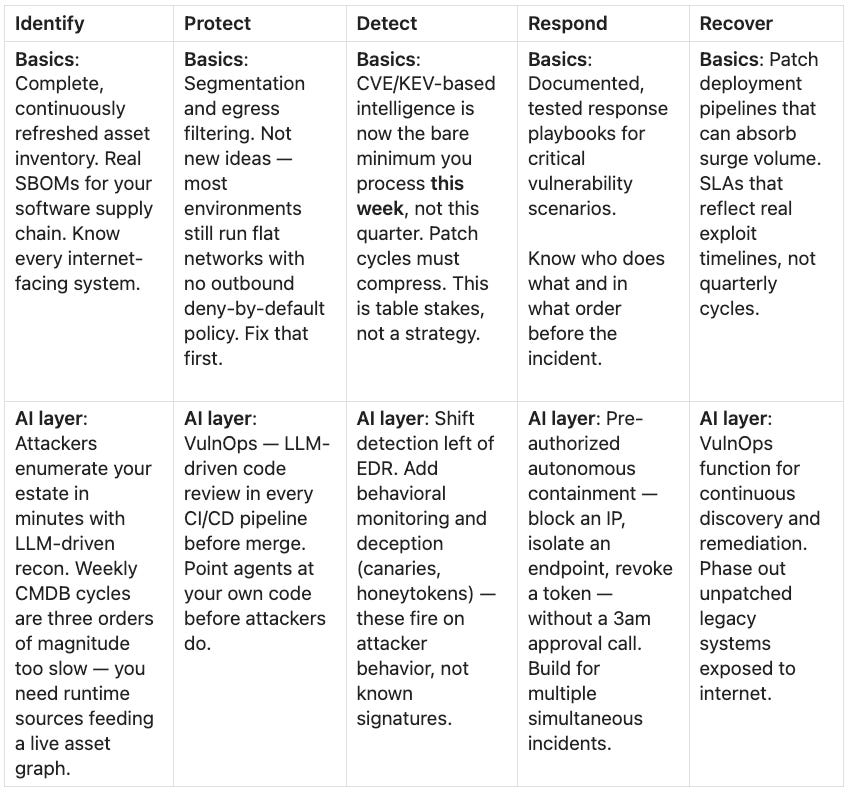
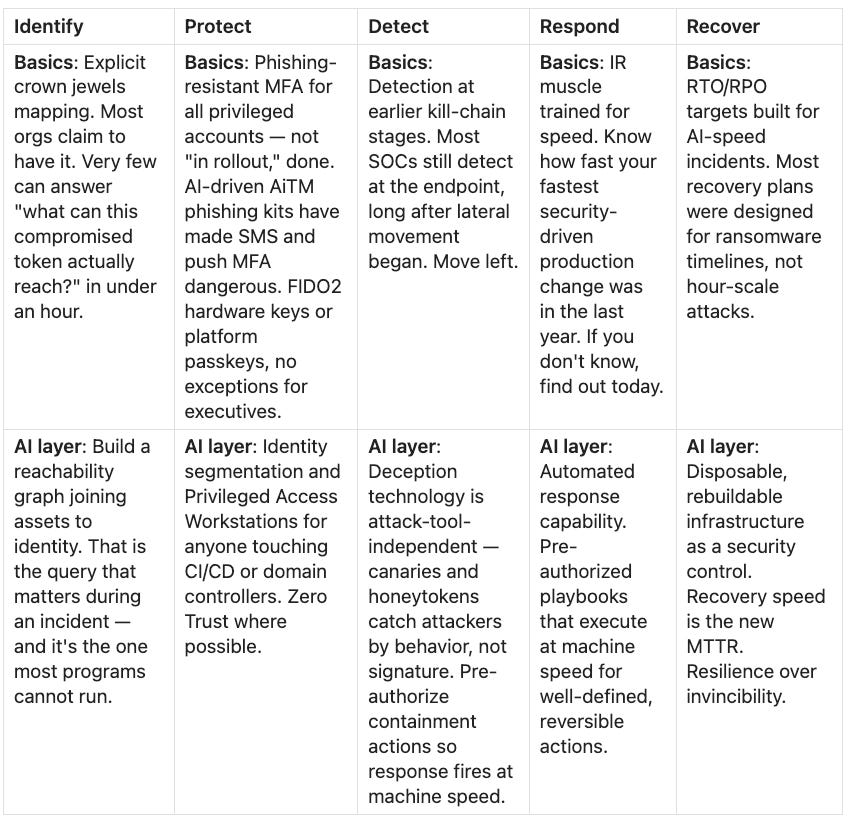
The threat map: AI acceleration across the NIST framework
To make the shift concrete, it helps to map where Mythos-class capabilities are changing the threat landscape. Drawing on Rob Fuller’s field brief and the CSA Mythos-ready guidance, the key issue is not that security fundamentals have changed, but that attacker speed, scale, and autonomy have.
The threats below show where that acceleration is now most visible. Three threats that are Mythos-class capabilities. For each, I separate the essential basics you need to address at scale from what AI adds.
Most security programs have not fully implemented the basics. Do not skip them.
Threat 1 — AI-powered zero-day discovery + exploit generation
Vulnerabilities found and weaponized in hours, not weeks
Threat 2 — AI-autonomous attacks at machine speed
Full attack chains (recon → exfiltration) running in hours
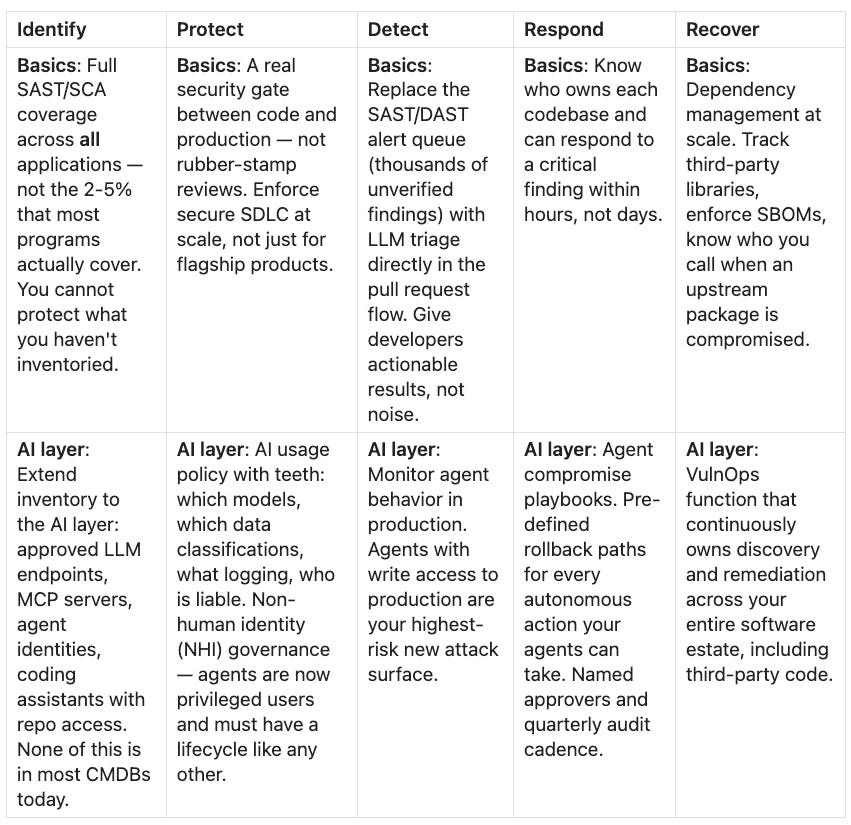
Threat 3 — AI-generated code and agentic supply chain
Coding agents shipping vulnerable code, unmanaged MCP servers, and compromised agents
What the program actually needs to change
Rob Fuller, VP of Information Security at a Fortune 500 company and Chair of the Vulnerability Management Research Group, wrote a sharp CISO field brief this April that cuts through the noise. I recommend reading it in full. His framing opens with this:
“I’ve spent twenty-five years on the offensive side of this business, and I’ve read most of the AI-and-security briefs of the last eighteen months. They’re mostly right about the threat and useless about what to do on Monday morning. ‘Improve asset management’ and ‘adopt Zero Trust’ insults a community that hasn’t been idle since 2015. We know. The question is what moves up, what moves down, what gets killed, and where the money goes.”
That is the right question. And his answer is worth quoting directly:
“Stop trying to outrun the rain with faster patching. Build a roof so that when it pours, the business stays dry.”
The cadence and volume of vulnerability disclosures are going to exceed anything we have seen. You cannot hire your way out. You cannot patch your way out. The answer is a program redesigned around resilience, automation, and the right priorities — not more analysts staring at dashboards.
Here is the short version of what moves, synthesized Fuller'sler’s brief and the CSA/SANS Mythos-ready program:
Here are areas that need urgent improvement:
Integrate AI agents into your security functions now. This should be standard practice, not an experiment. Agents already speed up incident response, code review, threat triage, and audit data collection. Every security role is shifting toward building with AI. The barrier to entry is low; if you know English, you can begin today.
Establish VulnOps as a permanent function. Do not rely on quarterly pen tests or a ticket queue. Build a team and pipeline for continuous vulnerability discovery and remediation across your environment, including third-party and open-source components. Treat this like DevOps, but focused on vulnerabilities.
Implement phishing-resistant MFA everywhere. AI-driven phishing kits have made SMS and push MFA unsafe. Use FIDO2 hardware keys or platform passkeys for all privileged accounts.
Apply deep segmentation. The Mythos preview showed that Linux kernel defense-in-depth was effective. Segmentation can turn an exploitable issue into one that is not exploitable in your environment. Use east-west segmentation, identity segmentation, and egress filtering as your main controls when patches are not yet available.
Increase governance speed. Set up a cross-functional process to evaluate threats and deploy defensive technology in days. Every approval delay gives attackers an advantage. As Fuller s”ys: “Every security exception that takes more than 48 hours to approve is a vulnerability you created your”elf.”
The CISO's mindset that this moment actually requires
I meet with about 300 CISOs each year. Most come from either consulting or audit backgrounds or have moved into cyber leadership for career growth.
Both backgrounds are valid, but neither prepares leaders for the current demands.
A Mythos-ready program is not an audit deliverable. It is an engineering challenge. Automating containment, deploying AI agents, building VulnOps pipelines, and enforcing governance at scale all require building, not just reviewing or reporting.
Security in 2026 needs a production mindset. Engineers design for repeatability, scale, and handling failures. Consultants produce one-off documents. The difference matters.
Audit skills still matter. Risk analysis, stakeholder communication, and compliance frameworks are important. But if your security leadership cannot build and run automated workflows, you will fall behind now.
The fastest-moving CISOs treat security like a software engineering team. They track deployment speed, not report completion. They build actionable playbooks and require agents at every level, holding teams accountable for using them.
Do not trust your own assumptions.
A recent conversation highlighted an important lesson.
A mature, well-resourced organization said it did not need to audit identity controls continuously. They believed their onboarding and offboarding process was solid, and everyone was accounted for.
We plugged in HARVEN — an agentic tool built for exactly this kind of continuous identity posture check.
We found that 20% of accounts were dormant, and some administrators lacked MFA. This happened in a mature organization with a process they trusted.
Do not assume controls are effective until you continuously check them. The basics are harder to maintain than expected, and the cost of missing them is higher than ever.
The bigger picture: who governs this?
I want to close with something beyond the operational. Bruce Schneier, who contributed to the CSA Mythos-ready brief, wrote a post that has stayed with me. He put it plainly:
“We need globally co-ordinated frameworks for independent auditing, mandatory disclosure of aggregate performance metrics and funded access for academic and civil-society researchers.
This has implications for national security, personal safety and corporate competitiveness. Any technology that can find thousands of exploitable flaws in the systems we all depend on should not be governed solely by the internal judgment of its creators, however well intentioned.
Until that changes, each Mythos-class release will put the world at the edge of another precipice, without any visibility into whether there is a landing out of view just below, or whether this time the drop will be fatal. That is not a choice a for-profit corporation should be allowed to make in a democratic society. Nor should such a company be able to restrict the ability of society to make choices about its own security.”
He is right. Organizations that act now by building resilient architectures, deploying defensive agents, and setting real AI policies will have more options when the next wave arrives.
Project Glasswing was a positive step. Anthropic gave 40 vendors early access to the patch before release. However, the global attack surface is much larger than any partner group can cover. As Mythos-class capabilities spread to more models, the window for coordinated disclosure gets smaller.
This is not a case against AI. It is a call to take operational work seriously and to push for industry and regulatory governance frameworks that meet current needs.
Do not wait for external changes. Begin your Mythos-ready plan this week.
Laurent 💚




This was incredibly well written! I really enjoyed where you went deeper into the, “okay here’s what you do on Monday morning” step by step!